SOC104 - Malware Detected
Difficulty: Medium
Type: SOC Alert
Alert Scenario
In this medium severity SOC alert on LetsDefend, we investigate a malware detection event triggered by a file with MD5 hash c74862e16bcc2b0e02cadb7ab14e3cd6. The alert originates from a Windows endpoint and involves analyzing sandbox reports, virus scans, and related logs to determine if it's a true threat or a false positive. We'll leverage platforms like ANY.RUN, VirusTotal, and Hybrid Analysis to examine the file's behavior, network activity, and indicators, while correlating with endpoint and proxy logs for context. This walkthrough emphasizes triage steps for malware alerts, including hash lookups, behavior analysis, and classification.
Investigation
Gathering Initial IOCs from the Alert
The alert provides the MD5 hash of the suspected malicious file: c74862e16bcc2b0e02cadb7ab14e3cd6. We start by searching for existing analysis reports on any.run using Google dorks to find submissions.
"c74862e16bcc2b0e02cadb7ab14e3cd6" site:any.run
Analyzing Sandbox Reports
ANY.RUN Analysis
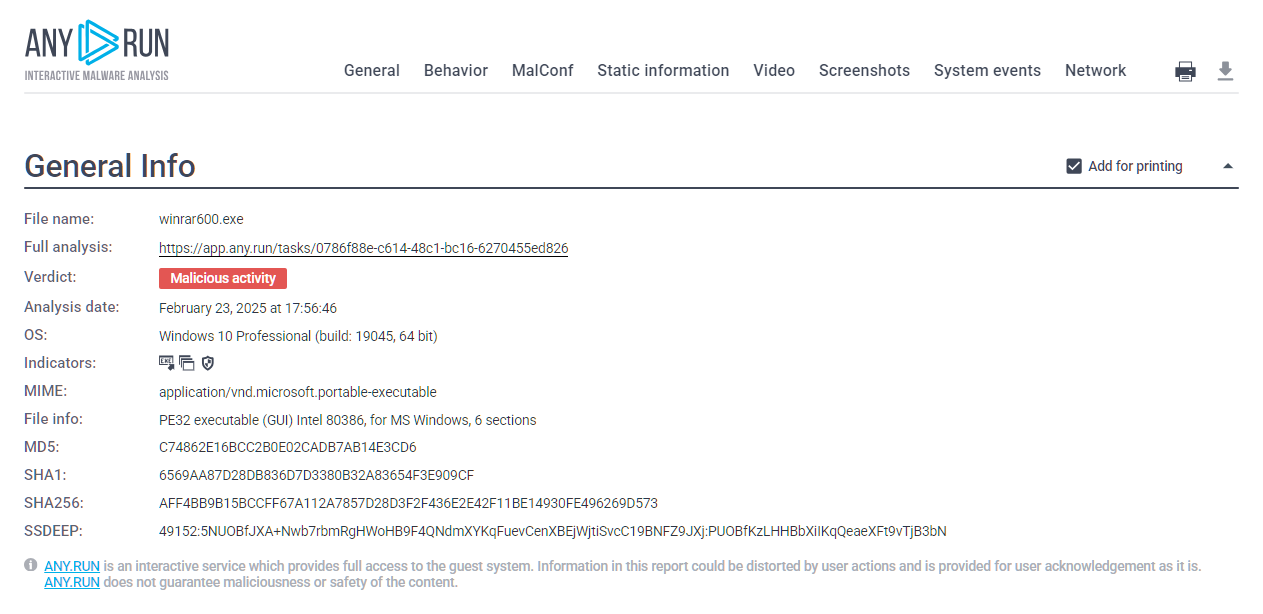
The above query reveals multiple reports. We'll focus on a recent one from February 23, 2025, at 17:56:46 UTC, which labels the file as winrar600.exe with a verdict of "Malicious activity," but requires deeper inspection.
ANY.RUN is an interactive malware sandbox that provides dynamic analysis, including process trees, network traffic, and MITRE ATT&CK mappings. Verdicts like "Malicious activity" can sometimes flag benign installers due to behaviors like registry modifications or network calls. Always correlate with IOCs like contacted domains and process details.
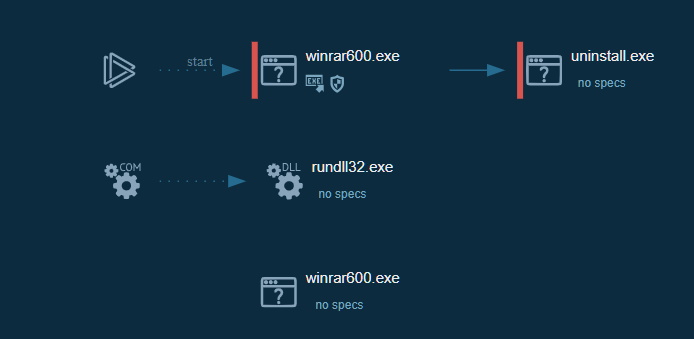
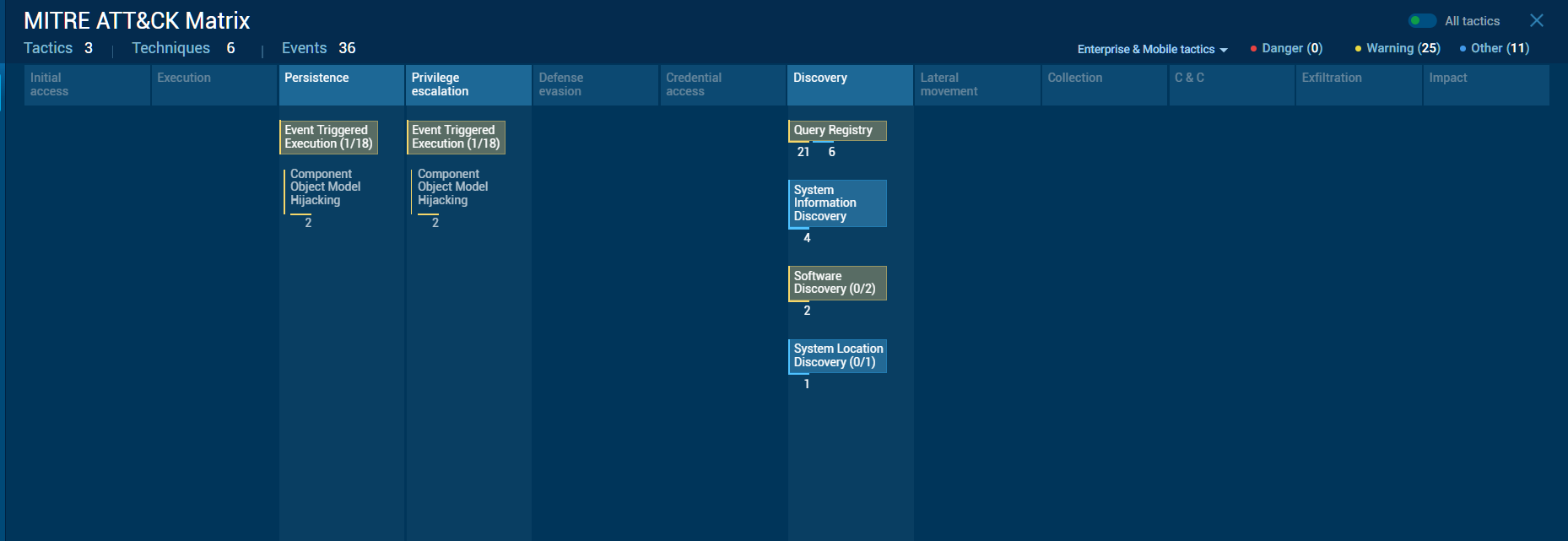
From the ANY.RUN report, the file is identified as a PE32 executable (GUI) for Windows, mimicking a WinRAR installer. Despite the "Malicious activity" verdict, key indicators suggest it's benign:
- Network activity: Contacted domains and IPs (e.g., win-rar.com) are whitelisted and legitimate.
- Processes: Spawned processes like
uninstall.exeandrundll32.exewith no suspicious specs, typical for installers.
-
MITRE ATT&CK: Only warnings for normal behaviors like:
- T1178 – Event Triggered Execution
- T1122 – Component Object Model Hijacking
- T1012 – Query Registry
- T1082 – System Information Discovery
- T1518 – Software Discovery
- T1614 – System Location Discovery
No dangerous tactics such as command-and-control, data exfiltration, or impact were observed.
References -
- https://any.run/report/aff4bb9b15bccff67a112a7857d28d3f2f436e2e42f11be14930fe496269d573/0786f88e-c614-48c1-bc16-6270455ed826
- https://app.any.run/tasks/0786f88e-c614-48c1-bc16-6270455ed826
VirusTotal Analysis
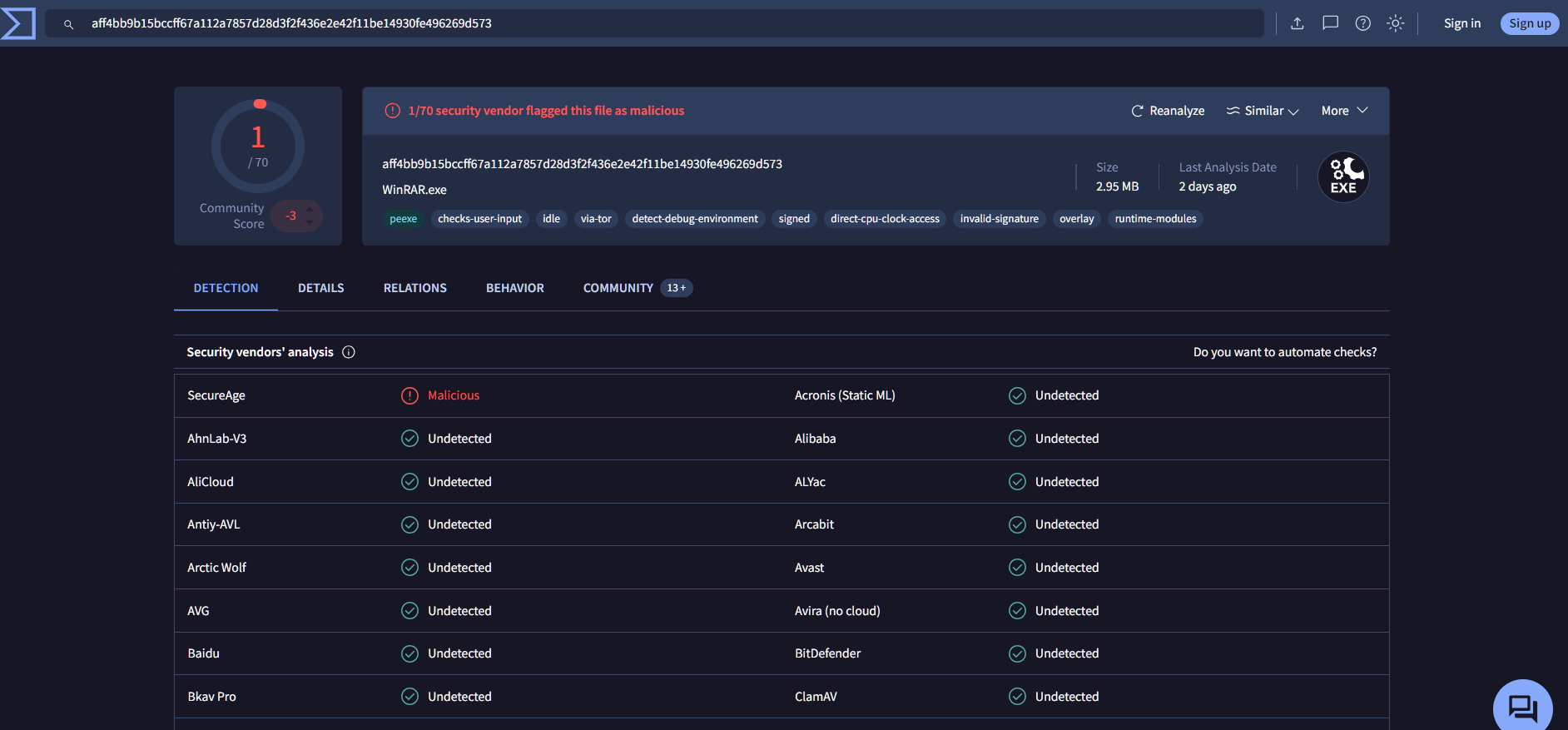
Next, we check VirusTotal for static analysis. The hash scores 1/70 detections, with only one vendor (SecureAge) flagging it as malicious—highly indicative of a false positive.
Hybrid Analysis
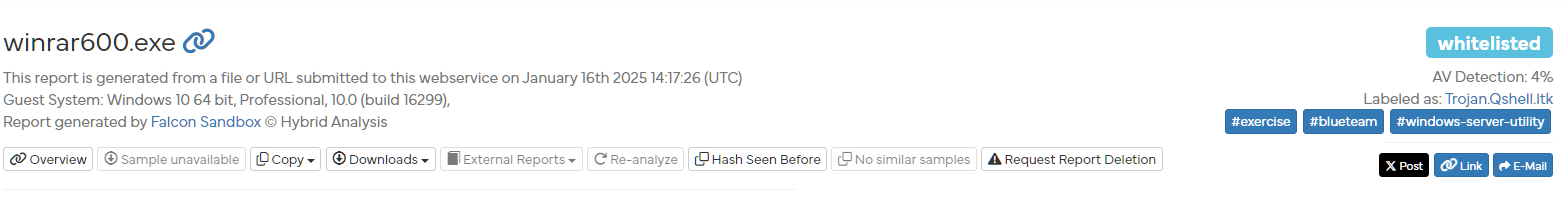
For further confirmation, we query Hybrid Analysis. All reports for the hash return a "whitelisted" threat level, with no malicious indicators in the most recent submission.

The platform confirms:
- No suspicious behavioral indicators
- No malicious dropped files
- No abnormal network communication
This further supports the conclusion that the detection is benign.
References -
Examining Endpoint and Proxy Logs
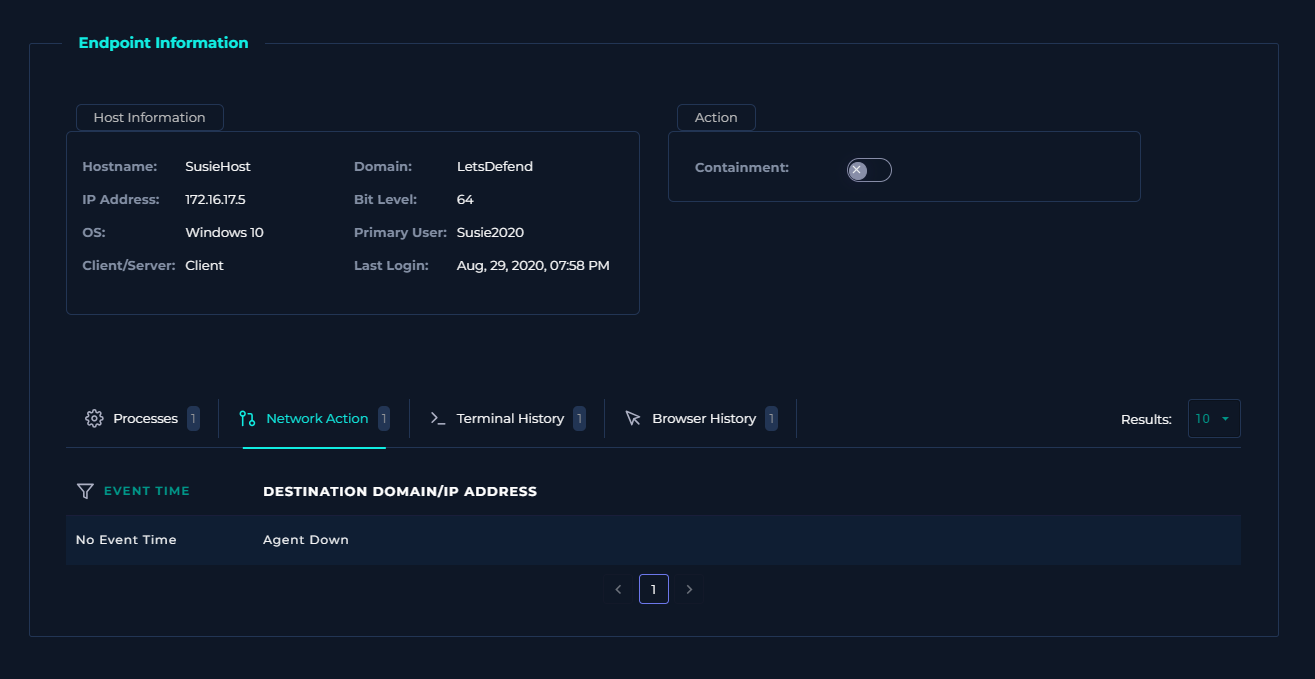
The alert originated from endpoint "SusieHost" (IP: 172.16.17.5, OS: Windows 10, Primary User: Susie2020). Checking the endpoint details shows no containment or quarantine actions taken.
The event timestamp is Mar 21, 2021, 01:04 PM. Reviewing subsequent logs reveals a proxy event two minutes prior:
type: Proxy
source_address: 172.16.17.5
source_port: 43213
destination_address: 51.195.68.163
destination_port: 443
time: Mar, 21, 2021, 01:02 PM
Request URL: https://www.win-rar.com/postdownload.html?&L=0&Version=32bit
Request Method: GET
Device Action: Allowed
Process: chrome.exe
Parent Process: explorer.exe
Parent Process MD5: 8b88ebbb05a0e56b7dcc708498c02b3e
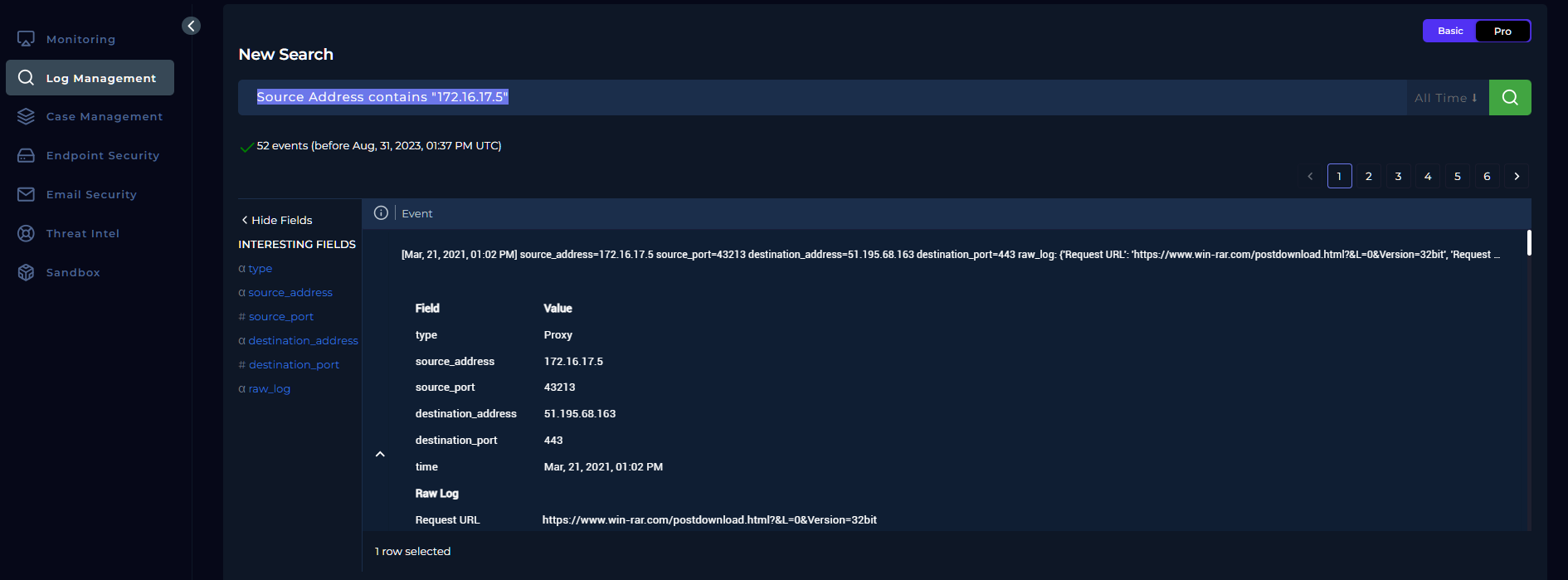
This indicates the file was downloaded via Chrome from the official WinRAR site, spawned from legitimate explorer.exe.
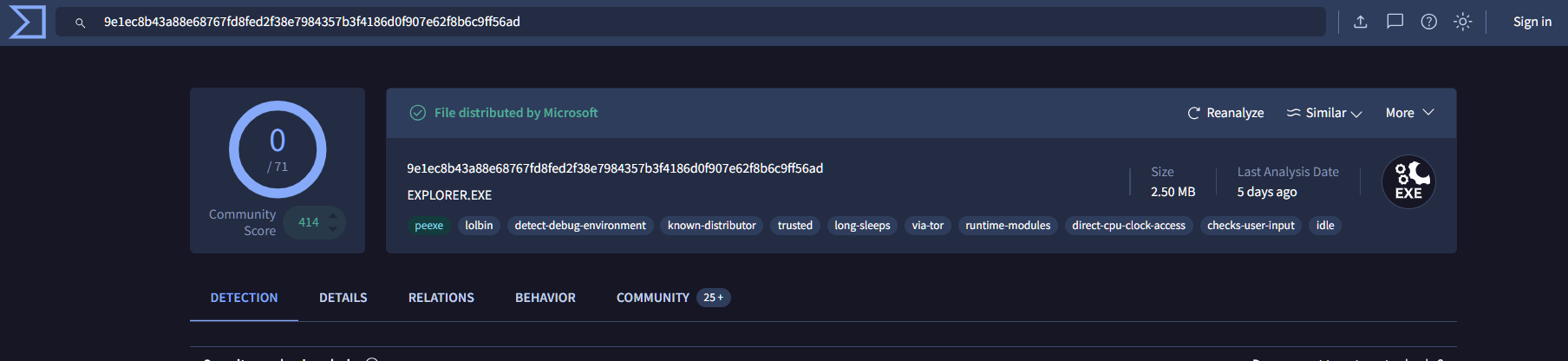
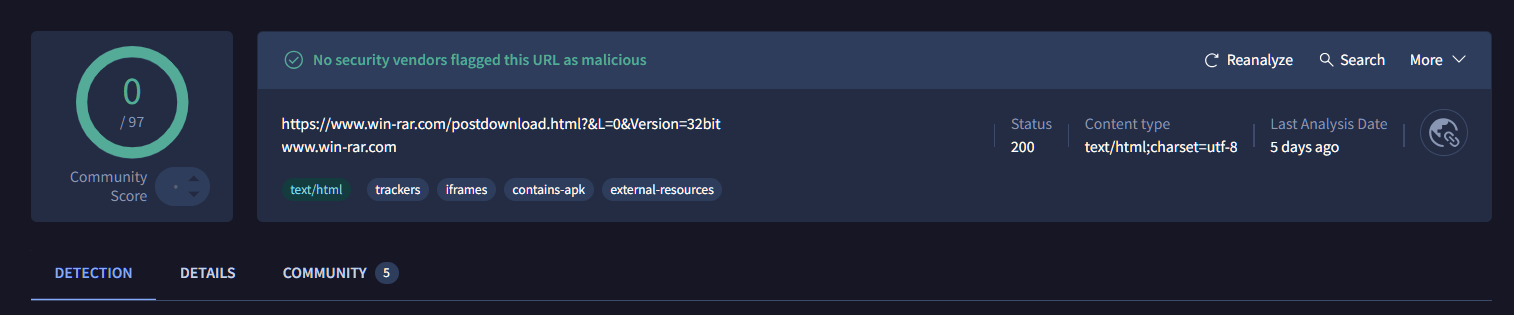
We validate additional IOCs on VirusTotal:
- Parent Process MD5 (8b88ebbb05a0e56b7dcc708498c02b3e): Clean, matches genuine Windows Explorer.
- Request URL (https://www.win-rar.com/postdownload.html?&L=0&Version=32bit): 0/97 detections, legitimate download page.
Although the ANY.RUN verdict says "Malicious," the lack of suspicious network traffic, dropped files, or anomalous processes and other subsequent indicators collected from VirusTotal and HybridAnalysis points to a false positive. The file is a legitimate WinRAR installer.
Classification and Closure
Based on the analysis, this is a false positive. The file is a benign WinRAR installer triggering alerts due to normal installer behaviors. We classify and close the case as follows:
- Define Threat Actor?
Other - Is the malware quarantined?
No - Is it malicious?
No - Is this a True or False Positive?
False Positive
MITRE ATT&CK Timeline
| Tactic | Technique |
|---|---|
| Execution | T1178 – Event Triggered Execution |
| Execution | T1122 – Component Object Model Hijacking |
| Discovery | T1012 – Query Registry |
| Discovery | T1082 – System Information Discovery |
| Discovery | T1518 – Software Discovery |
| Discovery | T1614 – System Location Discovery |
Artefacts
| IOC Type | Value | Description |
|---|---|---|
| File MD5 | c74862e16bcc2b0e02cadb7ab14e3cd6 | Hash of the detected file (winrar600.exe), confirmed benign |
| Request URL | https://www.win-rar.com/postdownload.html?&L=0&Version=32bit | Legitimate download URL from official WinRAR site |
| Parent Process MD5 | 8b88ebbb05a0e56b7dcc708498c02b3e | Hash of explorer.exe, clean and genuine Windows process |
| Source IP | 172.16.17.5 | Internal endpoint IP (SusieHost) |
| Destination IP | 51.195.68.163 | External IP for win-rar.com, whitelisted |
Attack Timeline Summary
Below you can find an Attack Timeline summarizing the chain of events on March 21, 2021:
| Time (Local) | Event |
|---|---|
| 01:02 PM | Proxy request to download winrar600.exe from official site via Chrome |
| 01:04 PM | Malware detection alert triggered on SusieHost |